HackTheBox – WifineticTwo
00:00 – Intro
01:00 – Start of nmap
02:54 – Discovering OpenPLC, looking for default credentials and logging in with openplc:openplc
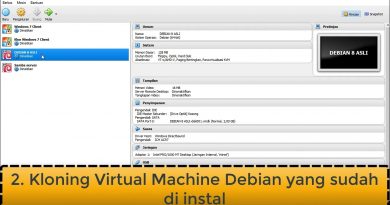
05:10 – Uploading a C reverse shell to OpenPLC
08:20 – Talking about our shell hanging our webserver, showing a POC that runs system() to background a process which seems to be smart
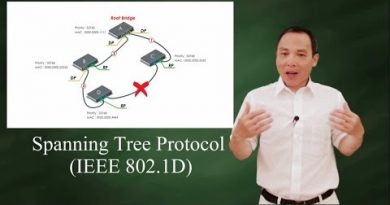
09:55 – Discovering a Wireless NIC, running IW to see wireless networks and OneShot to attack WPS
12:30 – Joining the Wireless Network, showing how important it is to tell DHCLIENT to not update default routes
16:55 – Cheating to get a root shell, so we can show the routing table of the container that can no longer talk to us
19:20 – Adding unset new_routers to a DHCLIENT Enter Hook so it doesn’t update routes
21:10 – Once we get on the Wireless Network we can SSH to OpenWRT and get the root flag
21:45 – Showing we could exploit OpenWRT through the web interface aswell, setting up a pivot with Chisel
23:20 – Logging into OpenWRT with a blank password, going to the Scheduled Tasks to create a cron
27:10 – Creating a Reverse Shell Payload with MSFVenom
29:20 – Getting multiple reverse shells so we can easily run multiple commands on the container
by IppSec
linux web server


THE GOAT
if you already have root access to the openplc router (via ssh), then why did you show the scheduled task thing?
quick tip for those weird default route situations. Route your machine IP via the box's current default gw explicitly. ip route add 10.10.x.x/32 via 10.0.3.1. That way no matter what extra default routes get added you won't lose access.
The great lesson
Hey Ipp, what are your thoughts on the implications of the falling price of gold on the global economy?
Hey Ippsec tried contacted you on linkedin but didn't get any repsonse i am just a beginner in this hack the box basically in cyber i wanna get started to solve machines like you do from where to start to get into pro like you
🇧🇩
Firsttt