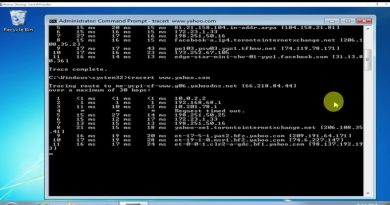
VLOG Thursday 369: Bitlocker Bypass, Bitwarden Passkeys, Some News, Home Lab, Tech Talk Live Q&A
Business Technicalities Channel
https://lawrence.video/biz
https://www.linkedin.com/in/lawrencesystems/
Connecting With Us
—————————————————
+ Hire Us For A Project: https://lawrencesystems.com/hire-us/
+ Tom Twitter 🐦 https://twitter.com/TomLawrenceTech
+ Our Web Site https://www.lawrencesystems.com/
+ Our Forums https://forums.lawrencesystems.com/
+ Instagram https://www.instagram.com/lawrencesystems/
+ Facebook https://www.facebook.com/Lawrencesystems/
+ GitHub https://github.com/lawrencesystems/
+ Discord https://discord.gg/ZwTz3Mh
Lawrence Systems Shirts and Swag
—————————————————
►👕 https://lawrence.video/swag
AFFILIATES & REFERRAL LINKS
—————————————————
Amazon Affiliate Store
🛒 https://www.amazon.com/shop/lawrencesystemspcpickup
Ubiquiti Affiliate
🛒 https://store.ui.com/?a_aid=LTS
Gear we use on Kit
🛒 https://kit.co/lawrencesystems
Try ITProTV free of charge and get 30% off!
🛒 https://go.itpro.tv/lts
Use OfferCode LTSERVICES to get 5% off your order at
🛒 https://lawrence.video/techsupplydirect
Digital Ocean Offer Code
��� https://m.do.co/c/85de8d181725
HostiFi UniFi Cloud Hosting Service
🛒 https://hostifi.net/?via=lawrencesystems
Protect you privacy with a VPN from Private Internet Access
🛒 https://www.privateinternetaccess.com/pages/buy-vpn/LRNSYS
Patreon
💰 https://www.patreon.com/lawrencesystems
CHAPTERS:
by Lawrence Systems
windows server dhcp



11:26 having a passkey stored in Bitwarden is no different security wise from having a TOTP code stored in Bitwarden. Passkeys were designed to be used on a single device, so 2FA was built in (you need both the passkey and the device). Once you save a passkey on a password manager it becomes single factor since any breach of the password manager gives access to the passkey without a second factor.
The most annoying about bitwarden passkey is that they can't be disabled… It always pops up before my yubikey gets addressed.
It's similar with hello windows… Had a hard time to couple my yubikey with some sites.
There is a lot to improve with passkeys
Where would I sign up for your newsletter?
I wanted to ask Tom about inter VLAN routing. You can restrict traffic with rules in pfsense but what if you have a clever managed switch, like a Qnap or Mikrotik with hardware accelerated packet switching, including vlans. Do you lose the ability to process rules on pfsense because the switch is allowing the packets to move between VLANs, or does the switch only transfer packets to the same VLAN? I'm thinking the switch, separate from pfsense, probably only moves packets between ports on the same vlan, and any packets from vlan a to vlan b would go via pfsense. Can anybody confirm. Could this be a useful teaching video. I have both Qnap 2.5g and Mikrotik 2.5g switches but I want to make sure IoT traffic cannot get to other vlans.
On the question of TOTP in Bitwarden…
First I use a ridiculously long, randomly generated password that I couldn't tell you even under the threat of death. I store the password offline in a couple secure places (primary, backup). Second, my Bitwarden second factor is a Yubico key. Excepting a massive vulnerability in Bitwarden, you're not getting into my vault without my master password and the (physical) Yubico key.
Ergo, excepting a few high value accounts that I use the Yubico key for, I store all my TOTP in Bitwarden and I sleep fine at night.
The one thing that I do that is a "risk" because I don't use a master password that I remember, is I set the timeout to never on systems that I use. This is a compromise in convenience vs. security, but I know every device that my BW is on, and I use drive encryption and strong passwords on those devices. Devices such as my phone would require you to have the ability to unlock my phone first and also unlock BW with Face ID. If a device is ever lost/stolen I can invalidate the sessions.
First
RE: Truenas Scale, I've had issues with App status not updating, especially when doing bulk updates. Otherwise it may be a session timeout.
I have two U6 enterprises and every time they do a firmware update I seem to have factory reset them and then readopt. It's very weird. All I can say is I'm glad they're not up stupid high and are easy to access.
It's important to note that modern devices shipped in the past 5yrs are no longer vulnerable to this Bitlocker attack as they feature firmware TPMs not discrete TPMs.
Combine passkeys with TOTP or yubikey and it is more secure than password + TOTP
The bit locker bypass was so amazing that it even appeared in the news